Introduction: The Evolution of a Question
For decades, intrusion detection systems (IDS) have operated on a simple premise: if a network packet matches a known attack pattern, raise an alert. This signature-based approach has been remarkably effective—against the attacks it already knows. But as threats grow more sophisticated, the question itself is changing. Instead of asking, "Does this match a known pattern?" modern systems are beginning to ask, "Does this actually make sense in context?" This shift is being driven by two key innovations: SnortML, a machine-learning extension for the popular Snort IDS, and agentic AI, autonomous agents that can reason and act independently.
The Limitations of Signature-Based Detection
Traditional signature detection works by comparing incoming traffic against a database of predefined signatures—binary fingerprints of known exploits, malware, or attack techniques. It's fast, reliable, and easy to deploy. Yet it has three critical weaknesses:
- Blindness to unknowns: Zero-day attacks, polymorphic malware, and subtle variations of known threats slip through undetected.
- High false-positive burden: Signatures must be constantly tuned to avoid flagging benign activity that merely looks like an attack.
- Context-free analysis: A signature match doesn't consider the broader environment—user behavior, network topology, or the sequence of events.
These shortcomings have long pushed the industry toward smarter, more adaptive methods.
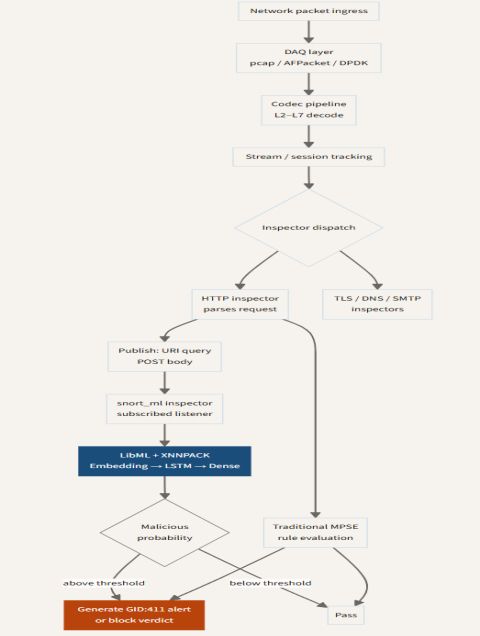
SnortML: When Rules Learn
SnortML is an open-source extension that integrates machine learning models directly into the Snort packet inspection engine. Instead of relying solely on static signatures, SnortML allows analysts to train models on normal traffic behavior and then deploy those models to identify anomalies in real time.
How It Works
At its core, SnortML uses a behavioral baseline. The system observes network traffic over a period, learning what's normal for that particular environment. It can capture patterns such as:
- Typical packet sizes and timing
- Protocol usage distributions
- Common destination ports and services
Once the baseline is established, SnortML compares live traffic against it. If a packet deviates significantly, the system flags it not because it matches a known threat, but because it doesn't belong. This approach catches novel attacks and subtle data exfiltration attempts that signature-based systems miss.
Advantages Over Signature-Only Systems
- Detection of zero-day exploits: No prior knowledge of the attack is needed; unusual behavior alone can trigger an alert.
- Reduced false positives: Context-aware models are better at distinguishing true threats from harmless anomalies.
- Adaptability: The system can be retrained periodically to reflect changes in the network.
However, SnortML is not a replacement for signatures—it's a complement. Most deployments use a hybrid approach: signatures catch known bad, machine learning catches unknown suspicious.
Agentic AI: Autonomous Defenders
Beyond machine learning models that merely analyze traffic, a new frontier is the use of agentic AI—autonomous software agents that can perceive, reason, and take action without human intervention. In the context of intrusion detection, these agents are designed to think like cybersecurity analysts but at machine speed.
From ‘Detect’ to ‘Respond’
Traditional IDS generate alerts and wait for a human to investigate. Agentic AI flips this model: when an anomaly is detected, the agent can:
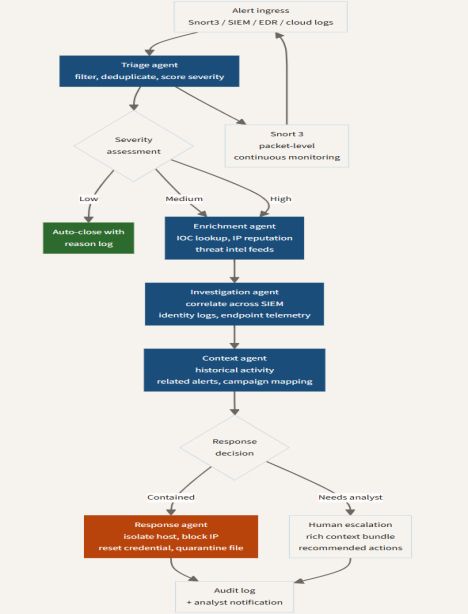
- Correlate the suspicious event with other data sources (e.g., system logs, user activity).
- Form a hypothesis about the nature of the threat—is this a lateral movement attempt? A data exfiltration? A false positive?
- Execute a containment action, such as isolating an endpoint, blocking an IP at the firewall, or terminating a suspicious process.
Importantly, these agents operate with contextual awareness. They understand the network's normal state and can distinguish between a benign deviation (e.g., a developer running a rare but legitimate script) and a true attack.
The Role of Multi-Agent Systems
In advanced deployments, multiple agents collaborate—each specialized in a different domain (network traffic, endpoint telemetry, user behavior). They share information and negotiate responses, mimicking a human team's distributed expertise. This approach reduces the cognitive load on human analysts and accelerates response times from hours to seconds.
Integrating SnortML and Agentic AI
The most powerful intrusion detection architectures combine the strengths of both approaches:
- SnortML provides a fast, low-level anomaly detection layer that can flag deviations from baseline behavior.
- Agentic AI sits above this layer, ingesting alerts from SnortML (and other sensors) to perform advanced correlation and autonomous response.
For example, SnortML might detect an unusual outbound data stream from a server that rarely initiates large transfers. The agent then queries the server's process list, sees an unfamiliar executable, and cross-references it with threat intelligence. If the executable is unknown and the beaconing pattern matches a known command-and-control technique, the agent can block the outbound traffic and escalate the incident to a human—but only after stopping the immediate threat.
Challenges and the Road Ahead
Despite these advances, context-aware detection is not a silver bullet. Machine learning models can be evaded by carefully crafted adversarial inputs, and agentic AI systems must be carefully constrained to prevent accidental damage. Organizations also face the ongoing challenge of data quality: models are only as good as the training data, and agents need reliable, comprehensive telemetry.
Nevertheless, the trajectory is clear. The question of intrusion detection is no longer just, "Is this packet malicious?" It's becoming, "What is the story behind this traffic?" And with tools like SnortML and agentic AI, defenders are finally starting to answer that question in real time.